How to Maximize Anti-Phishing Settings in Microsoft 365
Phishing attacks are becoming increasingly sophisticated, targeting businesses of all sizes. For IT administrators and security professionals, ensuring your organization's email security is robust isn't just a best practice—it's a necessity.
While Microsoft Defender for Office 365 (or M365) provides an array of security policies to consider, we'll focus on how to maximize its anti-phishing settings including what and how to configure, along with common challenges.
What to know about anti-phishing settings in M365
Microsoft Defender for Office 365 offers multiple layers of anti-phishing protection. Anti-phishing policies enable you to fine-tune protections and tailor settings according to your organization’s needs.
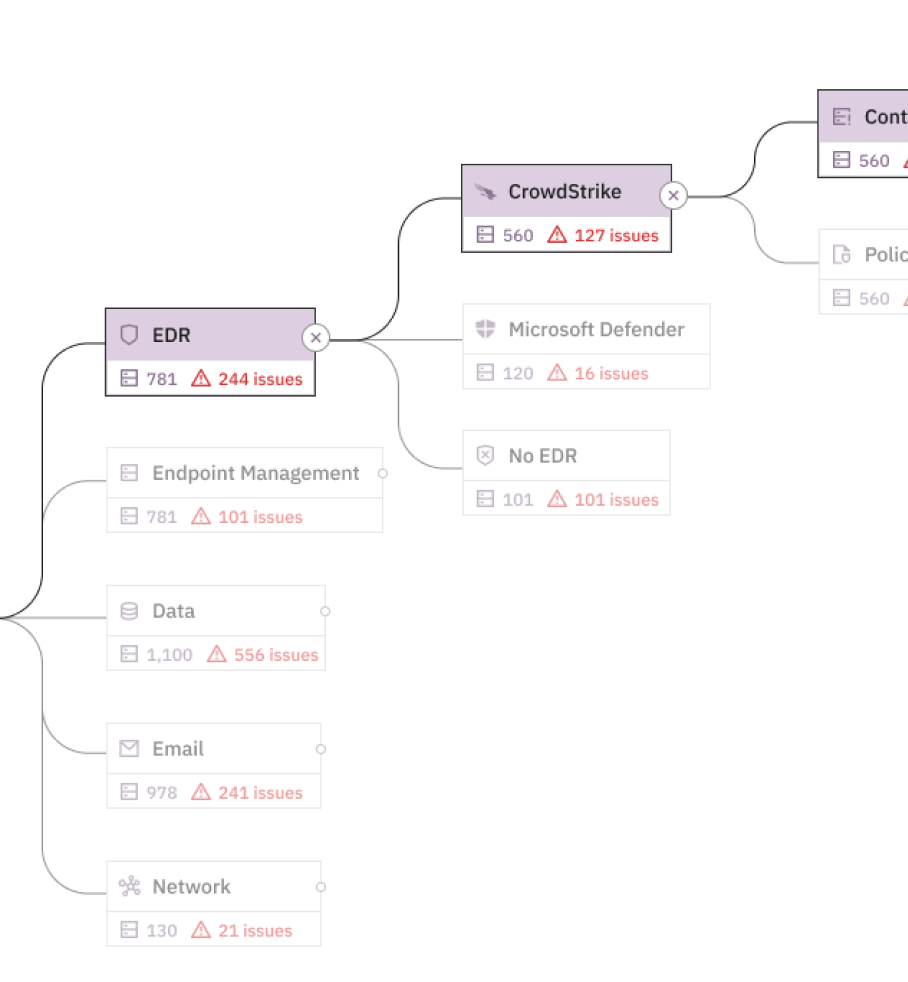
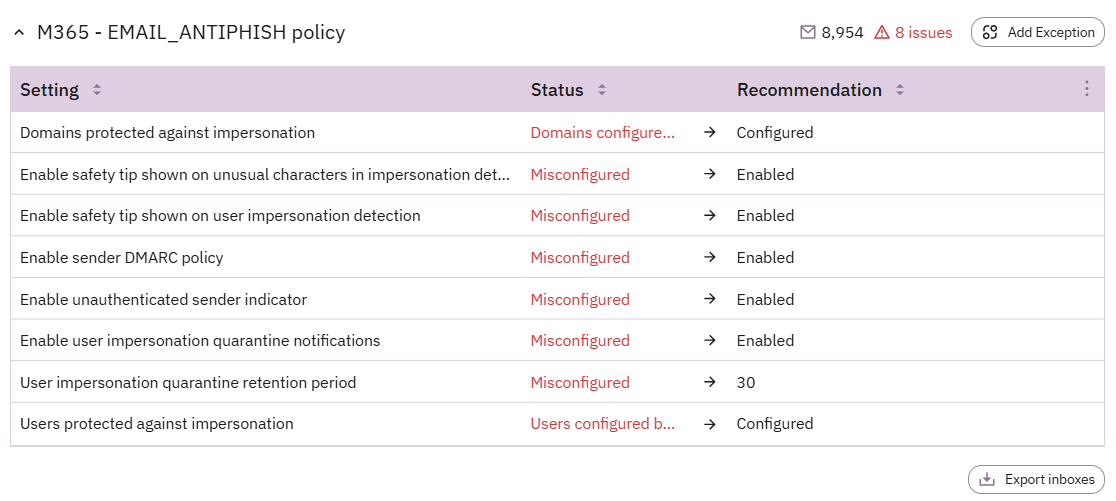
The default anti-phishing policy in Microsoft 365 is active for all users, but creating and customizing policies lets you add personalized safeguards for high-risk user groups, like executives, IT teams, or sensitive domains to maximize how the security tool you already have in place. In Prelude, we can track how these settings are enabled across inboxes and policies that may be included in your environment.
Impersonation Protection
Many of us have received the email from the CEO asking to buy gift cards. Impersonation attacks—where attackers masquerade as trusted individuals or brands—account for a vast amount of phishing incidents, including 89% of attempted attacks. Microsoft 365’s impersonation protection allows you to watch for and quarantine emails that mimic high-profile colleagues (e.g., the CEO) or your organization’s domains.
You can set this protection mode to “Automatic” (reliant on mailbox intelligence) or define protected users and domains manually. Adding executives, team leads, and all organization-approved domains to the protected list to maximize these settings.
Recommended configuration:
- Identify Protected Users (e.g., executives) and add them manually. Ensure domain protection includes all your organization’s domains.
- Opt for the Quarantine action for impersonated senders to ensure flagged emails never reach user inboxes.
Mailbox Intelligence
Mailbox intelligence studies historical email patterns to create a “contact graph” for each user. This enables the system to recognize unusual senders or email activity, flagging anomalies that deviate from regular correspondence.
Mailbox intelligence works seamlessly with impersonation protection. Together, they catch not just user fraud but also spear-phishing attempts from first-time senders pretending to be a known entity. While valuable for security, these settings typically work to reduce false positives by understanding typical user behavior before quarantining and alerting on emails that break from those patterns.
Recommended configuration:
- Depending on your team's ability to address quarantined emails, this setting is likely best enabled in groups to evaluate efficacy. Consider rolling this setting out based on high-activity, high-risk users and within that policy, toggle Enable Mailbox Intelligence and Enable Mailbox Intelligence Protection.
- By enabling these, flagged emails will be automatically quarantined for review.
Safety Tips
Microsoft’s safety tips visually alert users to potentially harmful emails and can be configured to display during certain scenarios such as:
- First contact alerts: Warns when you receive an email from a sender for the first time.
- Domain/user impersonation tips: Flags addresses similar to those of protected users or domains.
- Odd characters detection: Highlights suspicious Unicode characters used for visual deception (e.g., "prelud3security.com" instead of "preludesecurity.com").
These non-intrusive, educational cues make users a core part of your anti-phishing strategy and are among the lowest-lift settings to enable in your environment.
Spoof Intelligence and Authentication Indicators
Spoof Intelligence detects spoofing beyond standard email protocols like SPF and DKIM. Meanwhile, features like Unauthenticated Sender Indicators and “Via” Tagging add clarity to the email sender’s authenticity, empowering users to spot red flags.
Recommended configuration:
- Honor external senders’ DMARC policies with your settings. This stops spoofed emails from domains that fail DMARC checks.
- Set “Quarantine” or “Reject” as actions for emails failing DMARC to prevent exposure to harmful content.
Common issues with M365 anti-phishing settings
As with most security tools, configuration drift can occur. Regular monitoring is imperative to ensure existing settings are delivering the right outcomes without being inundated with false positives. If multiple anti-phishing policies are assigned to the same group, whether due to human error or dynamic grouping, conflicts can occur and the wrong settings may be enabled.
Monitoring policies and how they apply various settings to the individual, especially high-risk user groups, is an important aspect of what you can build in Prelude's monitoring platform. When it comes time to review the circumstances behind a greater volume of phishing emails getting through or a higher number of false positives, consider reviewing the following as well:
Phish Threshold Sensitivity
Available in Microsoft Defender for Office 365, this machine-learning capability informs how stringently your phishing policies are applied. Going higher may detect more threats, but is also likely to incur greater false positives.
Consider adjusting as you see more emails reach your users or deal with too many false positives. In combination with Mailbox Intelligence, false positives may be reduced at higher sensitivity.
Whitelisted domains
In the event of additional phishing attacks breaking through the existing policy, whitelisted domains or addresses in the Tenant Allow/Block List are a good first step in tuning your environment against more recent threats. These should be regularly reviewed as you collect more incident data.
Additional end-user control
If malicious domains are frequently getting through anti-phishing policies or users are subjected to more sophisticated attacks, disabling end-user controls is often a consideration for security teams. Policy Override settings in M365 allow end-users the ability to mark an email as safe, and is best left disabled, especially in your default policy group.
Third-party email gateways
Using a third-party email gateway before M365 can impact anti-phishing features. If the gateway routes email to M365, certain information, such as the original sender IP, may be lost, or the message may appear as if it’s coming from the gateway. Microsoft offers a feature called Enhanced Filtering for Connectors to ensure spoofing and authentication checks are applied correctly in these scenarios.
Proper configuration of this feature allows Microsoft’s anti-phishing and spoofing intelligence to function effectively. Additionally, the DMARC "Honor" setting will only work correctly if Microsoft can see the true sender domain, which enhanced filtering helps facilitate. If you use a third-party gateway, it’s important to follow Microsoft’s guidelines to avoid compromising these built-in protections and reducing the efficacy of the tool.
Making the most of your M365 security tools
With Microsoft 365’s anti-phishing tools, you don’t have to choose between convenience and comprehensive protection. By configuring policies for impersonation, leveraging mailbox intelligence, and enabling user-facing safety features, you create a multi-layered defense against today’s most sophisticated phishing attacks.
Security isn’t just about tools—it’s about getting them right. Take your setup further and ensure your configurations are optimized with a 14-day free trial of Prelude to understand how your M365 policies are currently configured and where there's room for improvement.
Start monitoring controls free for 14 days